Spain
(21 %)
Spain
(21 %)
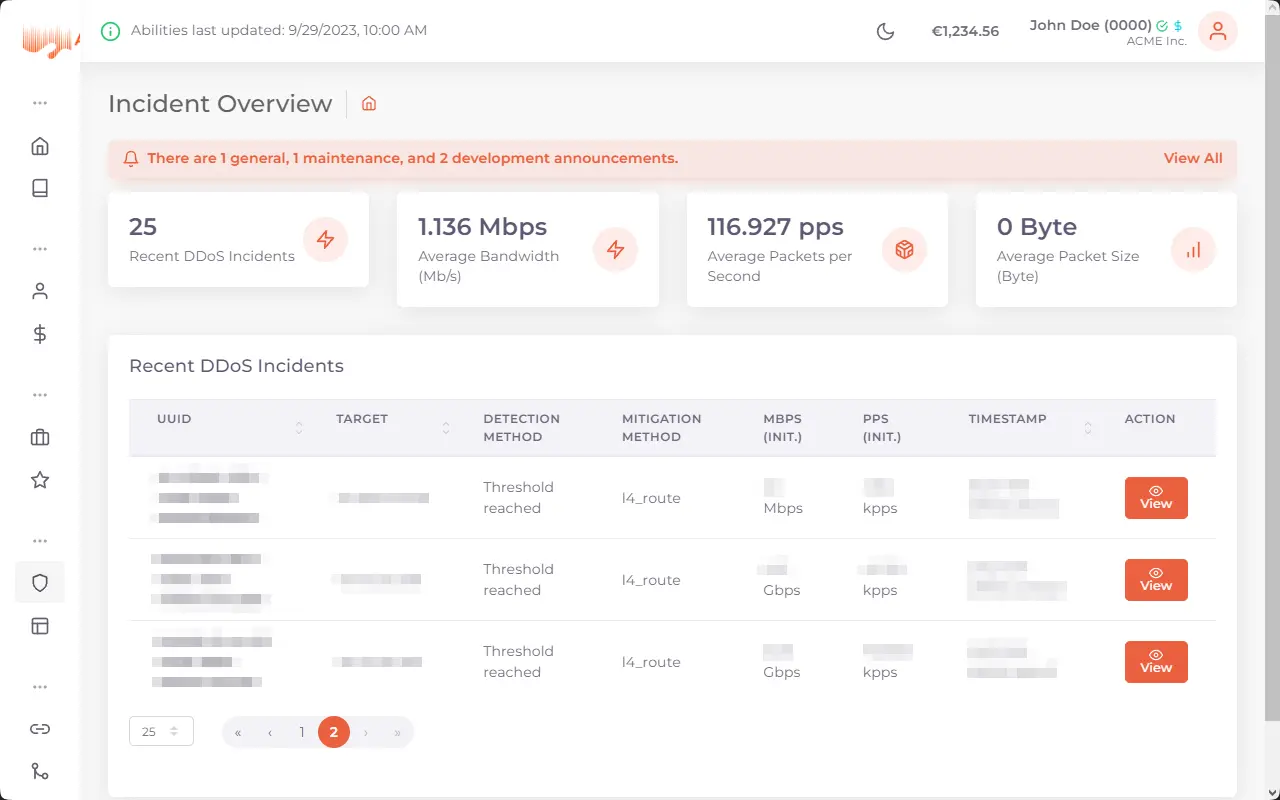
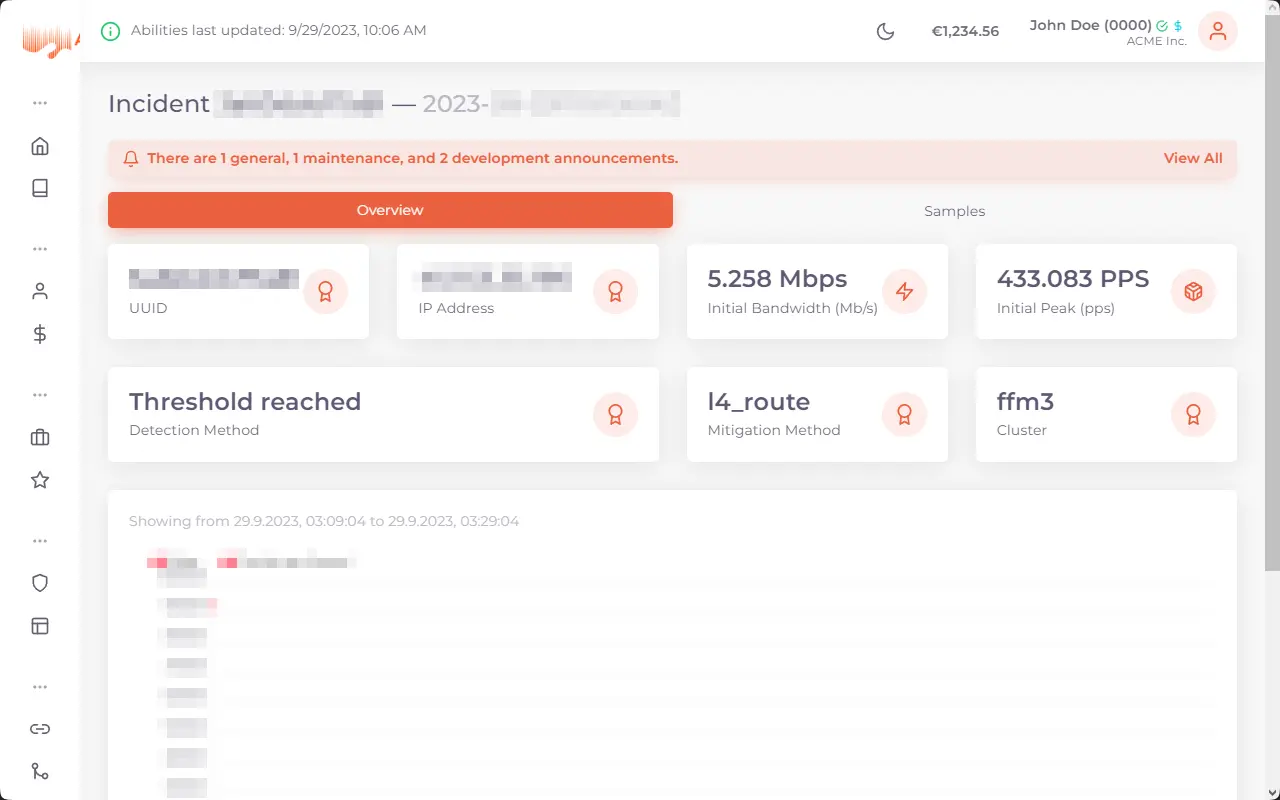
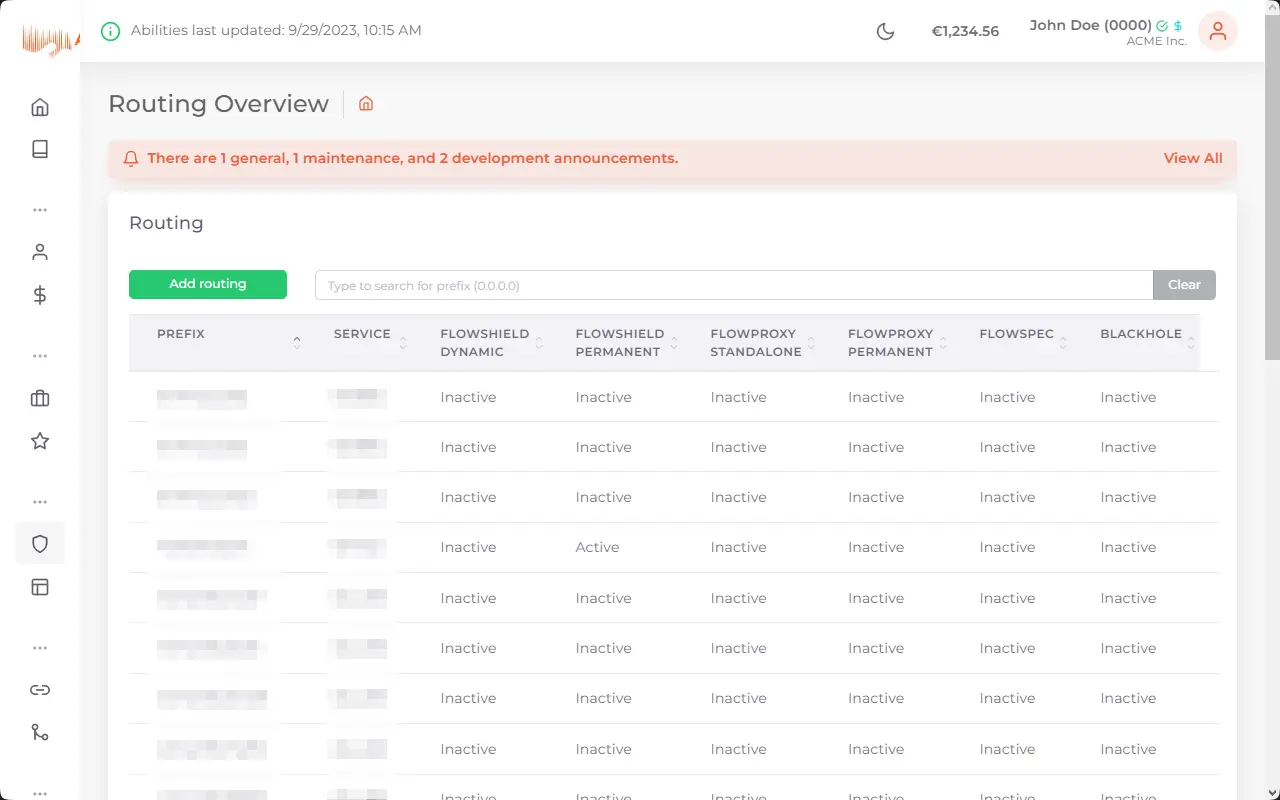
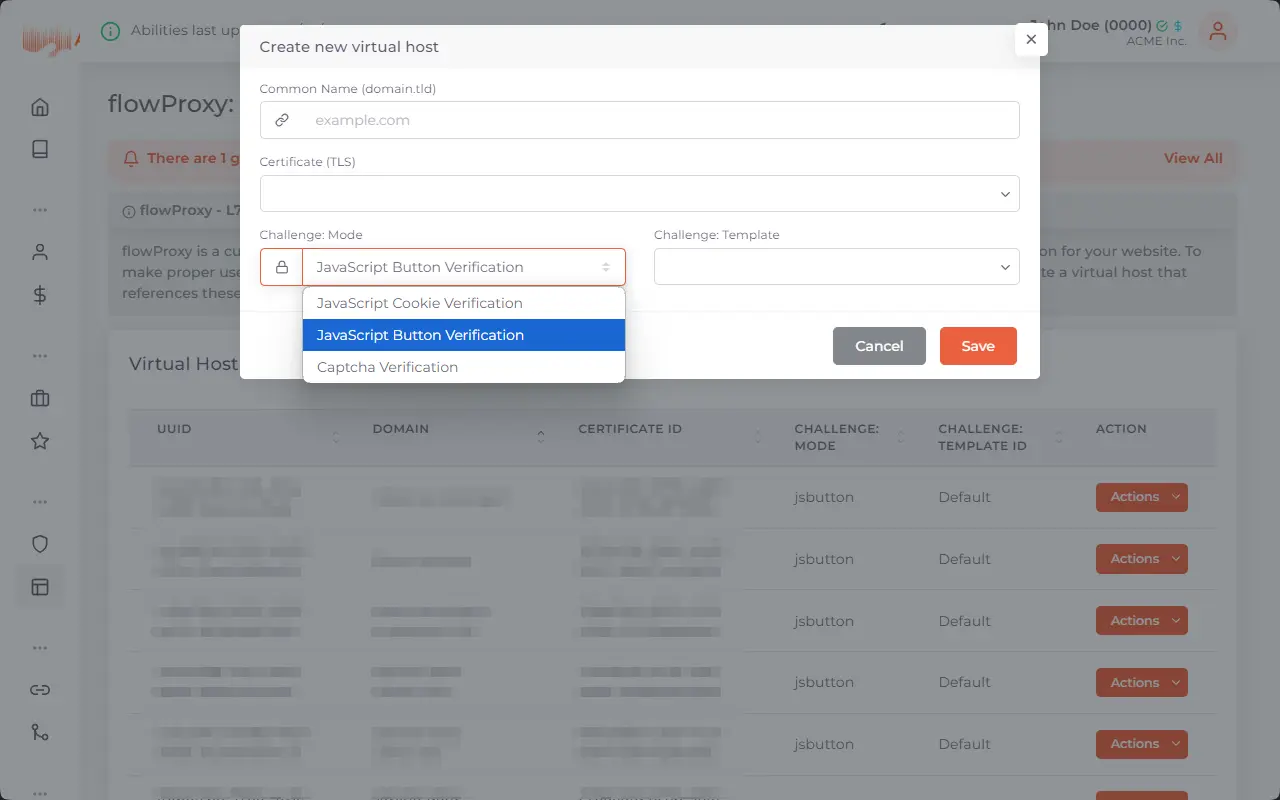
DDoS-Protection for your critical applications
Protect your services from malicious ddos attacks trying to render them offline. aurologic offers the most advanced, flexible and scalable DDoS-Protection solution.
Internet services are quite often targeted by ddos attacks, varying in size and complexity. We have built the most flexible and performant software stack, to automatically detect and block them, while keeping the attacked infrastructure online for legitimate clients.
 Latvia
(21 %)
Latvia
(21 %)
 Ireland
(23 %)
Ireland
(23 %)
 Netherlands
(21 %)
Netherlands
(21 %)
 Austria
(20 %)
Austria
(20 %)
 Greece
(24 %)
Greece
(24 %)
 Croatia
(25 %)
Croatia
(25 %)
 Luxembourg
(17 %)
Luxembourg
(17 %)
 Cyprus
(19 %)
Cyprus
(19 %)
 Estonia
(20 %)
Estonia
(20 %)
 Malta
(18 %)
Malta
(18 %)
 Poland
(23 %)
Poland
(23 %)
 France
(20 %)
France
(20 %)
 Lithuania
(21 %)
Lithuania
(21 %)
 Portugal
(23 %)
Portugal
(23 %)
 Romania
(19 %)
Romania
(19 %)
 Sweden
(25 %)
Sweden
(25 %)
 Czech Republic
(21 %)
Czech Republic
(21 %)
 Germany
(19 %)
Germany
(19 %)
 Hungary
(27 %)
Hungary
(27 %)
 Slovenia
(22 %)
Slovenia
(22 %)
 Belgium
(21 %)
Belgium
(21 %)
 Finland
(24 %)
Finland
(24 %)
 Italy
(22 %)
Italy
(22 %)
 Bulgaria
(20 %)
Bulgaria
(20 %)
 Denmark
(25 %)
Denmark
(25 %)
 Slovakia
(20 %)
Slovakia
(20 %)